Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
Security researchers have discovered a new type of "Man-in-the-Middle" (MitM) attack in the wild targeting smartphone and tablets users on devices running either iOS or Android around the world.
The MitM attack, dubbed DoubleDirect, enables an attacker to redirect a victim’s traffic of major websites such as Google, Facebook and Twitter to a device controlled by the attacker. Once done, cyber crooks can steal victims’ valuable personal data, such as email IDs, login credentials and banking information as well as can deliver malware to the targeted mobile device.
San Francisco-based mobile security firm Zimperium detailed the threat in a Thursday blog post, revealing that the DoubleDirect technique is being used by attackers in the wild in attacks against the users of web giants including Google, Facebook, Hotmail, Live.com and Twitter, across 31 countries, including the U.S., the U.K. and Canada.

|
Scooped by
Gust MEES
|
Spotify users, take note. The music streaming service just posted a message on its company blog indicating that one user's account was hacked, but assuring that steps are being taken to ensure others will not fall victim to the same exploit
Over the coming days, the Spotify Android app will prompt users to re-enter their username and password to log back in. Users running outdated versions of the app will be guided through the update process to ensure they’re running the latest version.
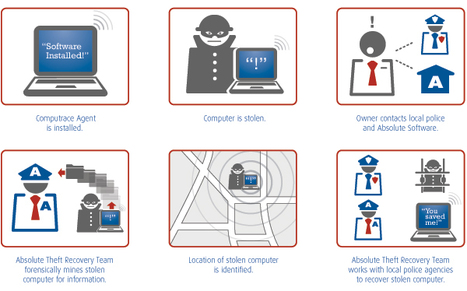
Et si je vous disais qu'il y a dans votre ordinateur un mouchard que vous ne pouvez pas enlever, qui a été mis en place par le constructeur, qui est sur les listes blanches de la plupart des antivirus et dont vous n'avez jamais entendu parler ? La société Kaspersky, spécialisée dans la détection et …
Via Frederic GOUTH, Gust MEES

|
Scooped by
Gust MEES
|
The Reveton ransomware gang is selling a version of CryptoLocker that can infect Android devices.
The version of the kit that’s being advertised by the Reveton gang has variants for victims in more than 30 countries, including the United States, UK, France, Germany, Australia and Spain.

|
Scooped by
Gust MEES
|
Millions of Android smartphones and tablets are at risk of being attacked via the Heartbleed bug, more than a week after the security vulnerability was first made public.
So, the obvious question you should be considering is, are you running Jellybean 4.1.1 on your Android devices?
Here’s how you can check: - Enter System settings
- Scroll the screen down to About
- Look for your Android version number
read more in the article...
Learn more:

|
Scooped by
Gust MEES
|
Researchers have uncovered a potentially massive attack on Android users. This highly elaborate ploy originates on Facebook, where cyber-criminals advertise a series of apps...

|
Scooped by
Gust MEES
|
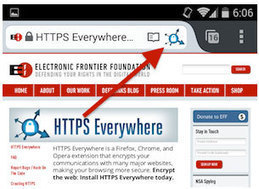
The Electronic Frontier Foundation (EFF) has announced the release of a beta version for its HTTPS Everywhere extension for Firefox on Android.
HTTPS Everywhere is produced as a collaboration between The Tor Project and the EFF.
The extension rewrites all requests to sites from HTTP to HTTPS whenever possible - i.e. it the website supports HTTPS in the first place - and by doing so increasing users' security and privacy. Until now, it was only available for desktop versions of Firefox, Chrome and Opera.

|
Scooped by
Gust MEES
|
The vulnerability could allow attackers to intercept traffic from Android devices despite an active VPN connection
A vulnerability in Android allows malicious applications to bypass an active VPN (virtual private network) connection and force traffic from the device through an attacker-controlled system where it can be intercepted, according to security researchers from Ben-Gurion University of the Negev in Israel.

|
Scooped by
Gust MEES
|
These days, the 2013 edition of the DefCamp security conference is taking place in Bucharest. There have been a lot of interesting presentations so fa... Alecu has found a vulnerability in Google devices that can be exploited to cause them to reboot.
The security hole impacts devices such as Galaxy Nexus, Nexus 4 and Nexus 5, regardless of the version of Android they’re running (even the latest KitKat)!

|
Scooped by
Gust MEES
|
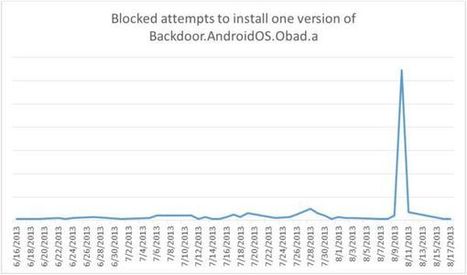
Google Cloud Messaging serving as conduit for sending data from C&C servers Criminals rent such networks to others for malware distribution. Among the malware distributed is the most sophisticated Android Trojan, known as Obad, Kaspersky said. The malware opens a backdoor in an infected device in order to download additional malicious code for stealing money from victims' bank accounts. While not common in the U.S., people in other countries often use their smartphone for money transfers.

|
Scooped by
Gust MEES
|
Die NSA hat laut einem Medienbericht Arbeitsgruppen für jedes große mobile Betriebssystem. Die Angreifer können Kontaktlisten, SMS, E-Mail und Aufenthaltsorte auslesen.

|
Scooped by
Gust MEES
|
Pour un conférencier de la Defcon 21, la fonctionnalité "weblogin" serait corruptible, et pas qu'un peu : tout un système applicatif pourrait être compromis en exploitant la bonne faille.

|
Scooped by
Gust MEES
|
Auf 75 Prozent aller Android-Geräte werkelt von der NSA entwickelter Code. Während die Behörde beteuert, damit nur die Sicherheit des mobilen Betriebssystems verbessern zu wollen, wittern Kritiker bereits einen neuen Schnüffel-Skandal.
|

|
Scooped by
Gust MEES
|
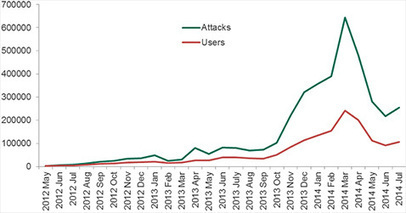
A total of 1,000,000 Android device users around the world encountered dangerous software between August 2013 and July 2014, according to the results of a survey carried out by Kaspersky Lab and INTERPOL. In fact, this period was the peak of cyber attacks registered in recent years.
The most popular malicious programs are SMS Trojans that send messages to premium rate numbers without the owner’s awareness.

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
We've recently found a vulnerability in certain Android apps that may leave user data at risk of being captured or being used to launch attacks.

|
Scooped by
Gust MEES
|
A critical security vulnerability has been found in Adobe Reader Mobile, the version of the popular PDF Reader developed for the Android operating system, which [...]
A critical security vulnerability has been found in Adobe Reader Mobile, the version of the popular PDF Reader developed for the Android operating system, which could lead to remote hackers compromising documents stored on your Android device and its SD memory card. If you were feeling smug that you had managed to avoid the Heartbleed flaw affecting up to 50 million Android users because you’re not running Android 4.1.1 of Jellybean, then perhaps you should wipe that smile off your face.

|
Scooped by
Gust MEES
|
Android-Entwickler wollen eine geheime Hintertür in Samsung-Galaxy-Smartphones entdeckt haben. Auch zwei von Samsung produzierte Nexus-Phones sollen betroffen sein.

|
Scooped by
Gust MEES
|
Cyber criminals can infiltrate your mobile devices with the just discovered first "TOR Trojan for Android".

|
Scooped by
Gust MEES
|
A new trojan for Android has been discovered that resides in the memory of infected devices and launches itself early on in the OS loading stage. Even if some elements of the threat ...

|
Scooped by
Gust MEES
|
A fake version of the popular Android game Minecraft - Pocket Edition is half the price of the real thing, but comes with a nasty surprise.

|
Scooped by
Gust MEES
|
Un chercheur a trouvé une méthode pour forcer les smartphones de la gamme Nexus de Google à redémarrer et ne pas se connecter au réseau. Il utilise une sorte d'attaques DDOS avec des SMS spéciaux.
The existence of another “master key” bug that can be used to push malware onto Android users has been publicly disclosed by Jay Freeman (a....

|
Scooped by
Gust MEES
|
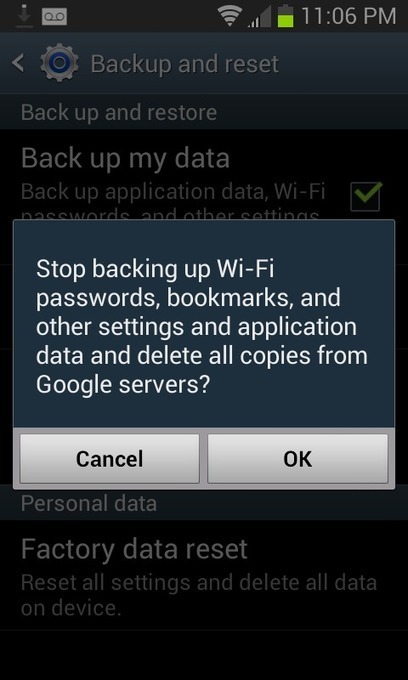
And the passwords are in plaintext, too. When you format an Android phone and set it up on first run, after you login to your Google account and restore your backup, it immediately connects to wifi using a saved password. There’s no sort of password hash that your Android phone could send your router to authenticate besides the password itself. Oh, and Google is part of NSA’s Prism program. If an NSA analyst, or likely someone from CIA or even FBI (Prism is a “team sport”), asks Google for information about you, your house’s and office’s wifi passwords are likely included in that data. Without a warrant.
|




 Your new post is loading...
Your new post is loading...