 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Picture the scene: you've had to hire a data protection officer, you've got a strict plan in place to notify all of your customers about breaches as soon as they happen, all of your data is encrypted and your company now has an insurance plan to help guard against data fines. This scene is in stark contrast to the security and compliance measures that many businesses currently operate under, yet this is expected to become standard practice, and the deadline to comply is fast approaching.
The European Union's Global Data Protection Regulation (EU GDPR) is expected to come into effect in 2017 and will transform how businesses approach compliance and data security. This newly proposed legislation will impact all organisations that process the personal data of EU citizens. So what does the compliant organisation of the not-so-distant future look like, and how can organisations ensure they meet these standards in time?
Mehr erfahren / En savoir plus / Learn more:
http://www.scoop.it/t/securite-pc-et-internet

|
Scooped by
Gust MEES
|
LinuxCon 2015 Security guru Bruce Schneier says there's a kind of cold war now being waged in cyberspace, only the trouble is we don't always know who we're waging it against.
Schneier appeared onscreen via Google Hangouts at the LinuxCon/CloudOpen/Containercon conference in Seattle on Tuesday to warn attendees that the modern security landscape is becoming increasingly complex and dangerous.
"We know, on the internet today, that attackers have the advantage," Schneier said. "A sufficiently funded, skilled, motivated adversary will get in. And we have figure out how to deal with that."
Using the example of last November's crippling online attack against Sony Pictures, Schneier said it was clear that many of these new attacks were the work of well-funded nation-states.
"Many of us, including myself, were skeptical for several months. By now it does seem obvious that it was North Korea, as amazing as that sounds," he said.
But what's troubling about many of these new attacks, he added, is that they can be hard to spot when they don't come in the form that security experts typically expect.
Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/securite-pc-et-internet/?tag=Cyberattack
http://www.scoop.it/t/securite-pc-et-internet

|
Scooped by
Gust MEES
|
Hackers don't even need your password anymore to get access to your cloud data.
Newly published research, released at the Black Hat conference in Las Vegas on Wednesday by security firm Imperva, shows how a "man-in-the-cloud" attack can grab cloud-based files -- as well as infecting users with malware -- without users even noticing.
The attack differs from traditional man-in-the-middle attacks, which rely on tapping data in transit between two servers or users, because it exploits a vulnerability in the design of many file synchronization offerings, including Google, Box, Microsoft, and Dropbox services.
Making matters worse, account owners are almost powerless. Because the tokens are tied to the user's device, changing the account password would not lock out the attacker.
Learn more / En savoir plus / Learn more:
http://www.scoop.it/t/securite-pc-et-internet/?tag=Cloud-Security

|
Scooped by
Gust MEES
|
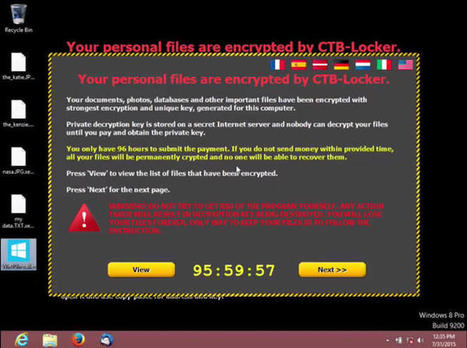
Just days after Microsoft released its latest operating system, hackers have begun targeting soon-to-be Windows 10 users with an emerging kind of malware.
Cisco security researchers are warning users against opening email attachments purporting to be from the software giant. The "ransomware" malware, which encrypts files until a ransom is paid, is being sent as part of an email spam campaign.

|
Scooped by
Gust MEES
|
Nachdem in den USA ein Jeep Cherokee über die Mobilfunkschnittstelle des Entertainment-Systems gehackt wurde, warnt die britische NCC Group: Autos lassen sich auch über Digitalradio (DAB) angreifen.
Mehr erfahren/ Learn more:

|
Scooped by
Gust MEES
|
The fact that a company called Hacking Team was hacked, combined with the disclosure of their shady clientele, has several diminished the credibility of previous denials the company has made about their engaging in this kind of profiteering. It also validates criticisms that groups like the EFF and Reporters Without Borders have thrown at Hacking Team – basically, that they provide agents around the globe with cyberweapons used for the suppression of democracy and the violation of human rights.
Hacking Team offers their clients a “Remote Control System” (RCS) that combines a variety of spyware technologies into one comprehensive surveillance suite. According to The Citizen Lab, this RCS product essentially allows users to do things like turn the microphones and cameras of their targets’ mobile phones on/off, monitor and record communications, and copy files and passwords.
While Hacking Team sells exclusively to governments, companies are designing products and services to give them similar capabilities.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Hacking+Team+breach
- https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/

|
Scooped by
Gust MEES
|
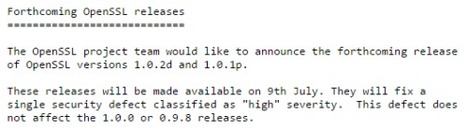
Sur le site du projet OpenSSL, il est conseillé aux administrateurs de se tenir prêts à appliquer un correctif de sécurité très important, qui sera diffusé le 9 juillet.
« Ce correctif sera diffusé le 9 juillet. Il va combler une faille de sécurité jugée hautement critique ». Voici ce qu’on peut lire dans l’annonce de la diffusion de ce futur patch, sur le site du projet OpenSSL.

|
Scooped by
Gust MEES
|
The U.S. Navy is paying Microsoft millions of dollars to keep up to 100,000 computers afloat because it has yet to transition away from Windows XP.

|
Scooped by
Gust MEES
|
Die kampfstarke US-Marine setzt nach wie vor auf Windows XP. Und zahlt dafür extra einige Millionen Dollar an Microsoft.
Erst kürzlich machte die Meldung die Runde, dass deutsche Behörden wie die Verwaltung von Berlin noch auf Windows XP setzen. Und mit der Benutzung des von Microsoft nicht mehr unterstützten Betriebssystems entweder gravierende Sicherheitslücken in Kauf nehmen oder aber Riesensumme für Extra-Support an Microsoft bezahlen.
Doch dieser Sonderweg einiger deutscher Bundesbehörden ist noch nichts gegen die Kriegsmarine der Vereinigten Staaten von Amerika, die sogar über U-Boote mit Atomwaffen verfügt. Denn auch die US-Marine setzt immer noch Computer mit Windows XP ein.

|
Scooped by
Gust MEES
|
Entdeckt haben sie Wissenschaftler der Technischen Universität Darmstadt und Experten des Fraunhofer-Institut für Sichere Informationstechnologie SIT. Die Daten landeten dort – etwa in Facebooks Parse und Amazons AWS - weil App-Entwickler Authentifizierungen für Cloud Services falsch verwenden. Betroffen sind E-Mail-Adressen, Passwörter, Gesundheitsdaten und andere persönliche Informationen von App-Nutzern.
Wissenschaftler der Technischen Universität Darmstadt und das Fraunhofer-Institut für Sichere Informationstechnologie SIT haben mehrere Cloud-Datenbanken untersucht und dabei rund 56 Millionen ungeschützte Datensätze gefunden. Dazu gehören neben E-Mail-Adressen auch Passwörter, Gesundheitsdaten und andere persönliche Informationen. Den Experten zufolge sind dadurch viele Nutzerkonten durch Identitätsdiebstahl und andere Internetverbrechen bedroht.

|
Scooped by
Gust MEES
|
Symantec Intelligence Report January 2015 [pdf] | CyberSecurity

|
Scooped by
Gust MEES
|
|

|
Scooped by
Gust MEES
|
The draft guide provides detailed example solutions using multiple products that achieve the same result, and instructions for implementers and security engineers, including examples of all the necessary components and installation, configuration and integration.
NIST notes that the draft guide also maps security characteristics to guidance and best practices from NIST and other standards organizations, and to North American Electric Reliability Corporation’s Critical Infrastructure Protection standards. The guide is modular and suitable for organizations of all sizes, including corporate and regional business offices, power generation plants and substations. They can adopt this solution or one that adheres to these guidelines in whole, or use the guide as a starting point for tailoring and implementing parts of a solution.
The draft guide can be found on the NCCoE Web site.
Learn more:
https://nccoe.nist.gov/projects/use_cases/idam

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
NICE Goals
NICE is a public-private partnership between government, academia, and the private sector. The mission of NICE is: “Cultivating an integrated cybersecurity workforce that is globally competitive from hire to retire, with the knowledge, skills, and ability to protect our nation from existing and emerging challenges.”

|
Scooped by
Gust MEES
|
Eight years ago researcher Dan Egerstad demonstrated how useful having your own Tor exit nodes can be if you want to spy on people by setting up five of his own.
He used them to harvest thousands of emails and messages from embassies in Australia, Japan, Iran, India and Russia, as well as the Iranian Foreign Ministry and the Indian Ministry of Defence.
He was running exit nodes rather than entry guards but his conclusion applies to both - he was convinced (although he provided no proof of it) that governments would surely be running or spying on Tor relays too:
I am absolutely positive that I am not the only one to figure this out ... I'm pretty sure there are governments doing the exact same thing. There's probably a reason why people are volunteering to set up a node.
Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/securite-pc-et-internet/?tag=TOR

|
Scooped by
Gust MEES
|
What about malware on Linux?
Here's how the argument might go if you were to ask that question:
Malware is impossible on Linux because Linux is secure by design, unlike Windows.
Even if Linux malware were possible, users would have to agree to run it, so that wouldn't count.
Even if users agreed to run it, they wouldn't be root, so that wouldn't count.
Even if they were root, who cares? There isn't any malware for Linux, so there.
The simple truth, of course, is that Linux is much more similar to Windows – in design, implementation and real-world security – than it is different.
As a result: there is malware for Linux; it can do plenty of harm even if you aren't root; and it may be able to infect without you realising.
Just like on Windows.
For all that, the "malware scene" on Linux simply never unfolded like it did on Windows, because the vast
Learn more:
http://www.scoop.it/t/securite-pc-et-internet/?tag=Linux

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
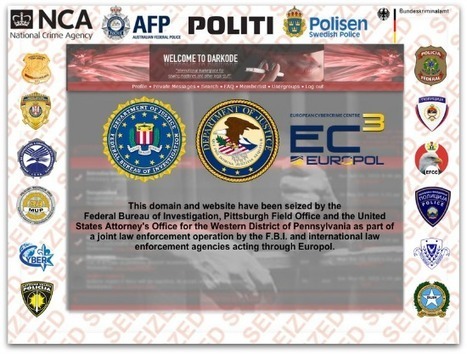
Darkode, a notorious cybercrime marketplace for malware, zero-day exploits, and botnets, was permanently shut down by a massive law enforcement operation coordinated between agencies in the US, Europe and elsewhere.
Learn more about Cybercrime:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=cybercrime

|
Scooped by
Gust MEES
|
Symantec has issued a warning about a successful scam being perpetrated against users of webmail services such as Gmail, Outlook and Yahoo.
The scam is explained in the following short video made by Symantec.

|
Scooped by
Gust MEES
|
Senior U.S. officials have said that the Chinese have begun in the last 12 to 18 months to build vast databases of Americans’ personal information for counterintelligence purposes. They have gone after such data contained not only in federal networks, but in systems belonging to health-insurance giants such as Anthem.
The breach details come as OPM leadership is under fire for its handling of a succession of network hacks over the last year and a half. The chairman of the House Oversight and Government Reform Committee, Rep. Jason Chaffetz (R-Utah), has called for the resignation of the agency’s director, Katherine Archuleta.
Under Archuleta, Wagner said, the agency in February 2014 began a program to identify vulnerabilities in the agency’s aging computer systems — some date to 1985 — and to modernize the network.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Cyberattack

|
Scooped by
Gust MEES
|
Viele Nutzer wissen aber laut Avast nicht, dass Hola sie selbst zu einem Exit Node für andere Hola-User macht. Das heißt, wenn etwa jemand über Hola auf illegale Inhalte zugreift, dann ist er eventuell mit Ihrer IP-Adresse im Internet unterwegs. Strafverfolgungsbehörden würden dann zuerst bei Ihnen anklopfen.
Des Weiteren verweist Avast auf eine Analyse von Vectra Research, laut der die Hola-Erweiterung weitere Programme auf Ihrem PC installieren kann – ohne dass Sie es bemerken.
„Browser-Erweiterungen sehen alles, was Sie im Browser sehen, inklusive aller Eingaben und Passwörter“, warnt Thomas Salomon von Avast. „Nicht vertrauenswürdige Erweiterungen können diese Daten leicht missbrauchen. Sie sollten deswegen sehr vorsichtig dabei sein, welche Erweiterungen Sie installieren“, so Salomon weiter.
Der Sicherheitsexperte empfiehlt Avast Browser Cleanup, um den Browser zu bereinigen.
Mehr erfahren / Learn more:
- http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=VPN

|
Scooped by
Gust MEES
|
This report was prepared by INSS and CSFI to create better cyber situational awareness of the nature and scope of threats to national security worldwide in the domains of cyberspace and open source intelligence. It is provided to Federal, State, Local, Tribal, Territorial and private sector officials to aid in the identification and development of appropriate actions, priorities and follow-up measures.

|
Scooped by
Gust MEES
|
Moskau/lngolstadt, 17. Februar 2015 Kaspersky Lab enttarnt die Cyberspionagegruppe „Desert Falcons“, die sich gegen verschiedene hochrangige Organisationen und Einzelpersonen im Nahen Osten richtet [1]. Damit konnten die IT-Sicherheitsexperten erstmals eine Gruppe von Cybersöldnern aus dem arabischen Raum enttarnen, die offenbar über das komplette Spektrum von Cyberspionagemitteln verfügt.
Die Gruppe startete ihre Aktivitäten bereits im Jahr 2011, seit dem Jahr 2013 werden Rechner infiziert. Den Experten von Kaspersky Lab zufolge erreichte die Kampagne ihren Höhepunkt zu Beginn des Jahres 2015 [2].
|



 Your new post is loading...
Your new post is loading...























.
Learn more:
.
http://www.scoop.it/t/securite-pc-et-internet/?tag=Internet+of+things
.
https://globaleducationandsocialmedia.wordpress.com/2014/01/21/why-is-it-a-must-to-have-basics-knowledge-of-cyber-security-in-a-connected-technology-world/
.