 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
The Wild Neutron hacking group gained access to an internal database Microsoft uses to track software vulnerabilities.
David Bisson reports. On 17 October 2017, five former employees revealed that at the time of the breach Microsoft raised a number of internal alarms signaling that hackers had compromised the database it uses to track patches. The attack has been blamed on Wild Neutron, a sophisticating hacking group which has targeted Apple, Facebook, and a number of other multi-billion dollar companies. Even so, the former Microsoft workers said the database was poorly protected by just a single password. Concerned that the hacking group had stolen details on some of its open vulnerabilities for Windows and other software, Microsoft decided to look at other industry breaches and investigate the timing of those event with respect to when the flaws entered its database. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?&tag=DATA-BREACHES

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Patch Tuesday has been and gone, which means that if you're responsible for the security of the computers in your office - or the ones you use at home - it's time to update your systems once again.

|
Scooped by
Gust MEES
|
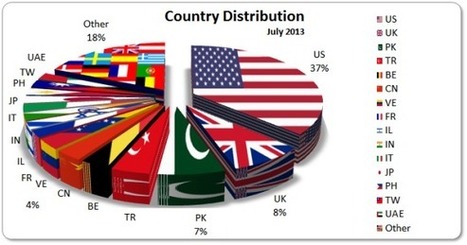
It's time for the Statistics related to the Cyber Attacks reported in the July 2013 Timelines (Part I and Part II). You will find a (hopefully) welcome novelty from this month: as a matter of fact ...
LinkedIn is working on its right-on-the-ball-with-security reputation, this time letting slip its domain details. According to this App.net post: “LinkedIn just got DNS hijacked, and for the last hour or so, all of your traffic has been sent to a network hosted by this company [confluence-networks.com]. And they don't require SSL, so if you tried to visit, your browser sent your long-lived session cookies in plaintext.” (User @berg)
Venez defier les meilleurs hackers, dans une course contre la montre sans merci
Download the 2013 #DBIR from Verizon for the latest on data security threats.

|
Scooped by
Gust MEES
|
HP : les vulnérabilités sont en hausse de près de 20% Principales conclusions de cette étude :
• Les vulnérabilités totales sont en progression
o les divulgations de sécurité ont augmenté de 19 %, passant de 6 844 en 2011 à 8 137 en 2012 ;
o le nombre de divulgations annoncées en 2012 reste inférieur de 19 % au record atteint en 2006 ;
• Les vulnérabilités critiques ont régressé, mais représentent encore un risque significatif :
o Les vulnérabilités critiques sont passées de 23 % en 2011 à 20 % en 2012 ;
o Une vulnérabilité sur cinq permet encore aux agresseurs de prendre le contrôle total de leur cible ;
• Les vulnérabilités Web bien connues se taillaient encore la part du lion en 2012 :
o Quatre catégories de vulnérabilités Web représentaient 40 % des incidents publiés en 2012 ;
• Les vulnérabilités exploitées par détournement de clics (clickjacking) sont encore omniprésentes :
o Moins de 1 % des adresses (URL) testées bénéficient d’une mesure d'atténuation standard, après plus d'une décennie ;
• Le taux de vulnérabilités mobiles continue d'augmenter rapidement :
o Les vulnérabilités mobiles ont progressé de 68 %, passant de 158 en 2011 à 266 en 2012 ;
o 48 % des applications mobiles testés en 2012 ont accordé un accès non autorisé.
• Les technologies matures introduisent des risques continus et évolutifs :
o Les vulnérabilités identifiées dans les systèmes SCADA (Supervisory Control And Data Acquisition) ont augmenté de 768 %, passant de seulement 22 en 2008 à 191 en 2012.
Les clients peuvent être opérationnels en quelques minutes, bénéficiant rapidement d’une vision précise des menaces de sécurité potentielles en exploitant des informations issues de plusieurs centaines de sources de données. La solution surveille également l'activité des applications et des utilisateurs, en quête d’anomalies de sécurité, telles que des comportements suspects.

|
Scooped by
Gust MEES
|
Die jährlichen Auszeichnungen für grobe Fehlleistungen bei Datenschutz und Privatsphäre gehen 2013 an Apple, Google, die Deutsche Post und die Bundespolizei sowie an die deutschen Ministerpräsidenten.
As expected Microsoft released seven important and two critical fixes for Windows, Internet Explorer and other Microsoft products. Adobe followed suite releasing fixes for ColdFusion, Flash and Sho...

|
Scooped by
Gust MEES
|
Face à l’attentisme et au mutisme de Google sur les nouvelles règles de confidentialité, six CNILs européennes, dont...
|

|
Scooped by
Gust MEES
|
The largest hack in history just got three times worse for Yahoo. "Following an investigation with the assistance of outside forensic experts, [we believe] that all Yahoo user accounts were affected by the August 2013 theft," Suzanne Philion, an Oath spokeswoman, said in a statement Tuesday. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?&tag=DATA-BREACHES

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
There's more fallout for the RSA Conference after its namesake's dealings with the NSA were brought to light.

|
Scooped by
Gust MEES
|
Just days after the launch of the PlayStation 4 and the Xbox One, Kaspersky Lab experts have discovered that PC gamers across Europe were hit by a massive number of attacks in 2013. Currently Kaspersky Lab knows 4.6 million pieces of gaming focused malware, with the total number of attacks facing gamers hitting 11.7 million globally. ===> On average, users were hit by 34,000 attacks related to gaming malware daily. <===

|
Scooped by
Gust MEES
|
Eine chinesische Hacker-Gruppe soll laut Symantec Kundenaufträge für Cyber-Attacken rund um den Globus ausgeführt haben. Die Gruppe soll hauptsächlich US-amerikanische Organisationen angreifen, um Informationen zu stehlen.

|
Scooped by
Gust MEES
|
Hack.lu is an open convention/conference where people can discuss about computer security, privacy, information technology and its cultural/technical implication on society. The aim of the convention is to make a bridge of the various actors in the computer security world. The conference takes place at Parc Hotel Alvisse in Luxembourg the 22-24 October 2013.

|
Scooped by
Gust MEES
|
The amount of cybercriminal activity associated with the Zeus family of financial Trojan programs has increased during the past few months, according to security researchers from antivirus vendor Trend Micro.
Bösartige Angreifer kapern Apache-Webserver und leiten deren Besucher auf Schad-Websites um. Die Tarnung der Malware ist fast perfekt. Eine Hintertür, die von Administratoren nur schwer bemerkt werden kann, sorgt dafür, dass Internet-Anfragen an Apache-Server nicht in Logs aufgenommen werden. Die gesendeten http-Anfragen, die in Wirklichkeit einen Trojaner steuern, sind nicht ersichtlich. Der Rest des Angriffs läuft im Speicher ab, Bugfixes gibt es noch nicht. 29. April 2013 von Manfred Kohlen 0
Die Malware Linux/Cdorked.A ist eine raffinierte Hintertür, die alles tut, um den Internetverkehr auf schädliche Webseiten umzuleiten, schreibt Sicherheitsanbieter Eset in einer aktuellen Warnung. Der Schädling sei so gut, dass er laut eigener Analysen schon hunderte von Webservern unter seine Kontrolle gebracht habe.
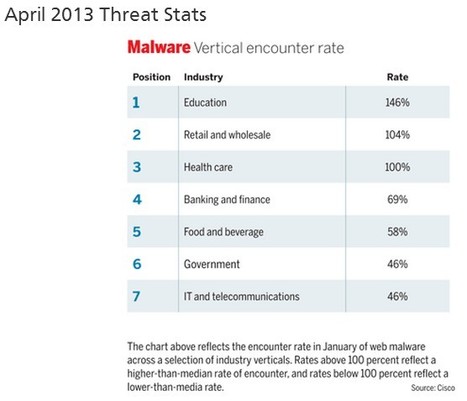
According to this month's threat stats, the total number of records containing sensitive data involved in breaches in the U.S. since January of 2005 is 607,255,063
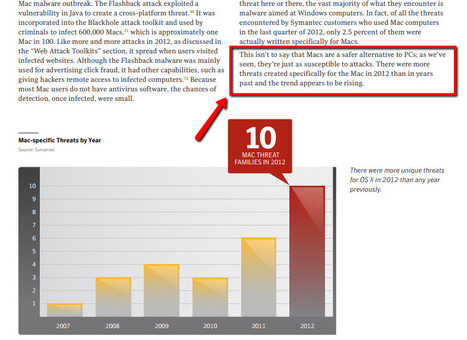
Mac's are NOT a safer alternative to PC's! Rising number of unique threats for OS X in 2012
"Everything is connected" ENISA has launched its new corporate video clip. This six-minutes movie describes the role of ENISA in a world where "everything is connected" both privately and professionaly. Communication technology connects us to family, friends, banks, and other private and e-government services we all rely on. But the Internet is under constant threat, from crime, attacks and accidents. Spamhaus, Stuxnet, Flamer, High Roller to name a few of the sophisticated cyber-attacks that took place the last 3 years. It is the European Union Agency ENISA’s job to work with prevention at EU levels in the field of cyber security. ENISA is working with governments, regulators and industry to assess risks and identify practical solutions to keep business, citizens and economy secure. This way, we support the smooth functioning of Europe’s internal market.
Via Gust MEES
|



 Your new post is loading...
Your new post is loading...
























On 17 October 2017, five former employees revealed that at the time of the breach Microsoft raised a number of internal alarms signaling that hackers had compromised the database it uses to track patches.
The attack has been blamed on Wild Neutron, a sophisticating hacking group which has targeted Apple, Facebook, and a number of other multi-billion dollar companies.
Even so, the former Microsoft workers said the database was poorly protected by just a single password.
Concerned that the hacking group had stolen details on some of its open vulnerabilities for Windows and other software, Microsoft decided to look at other industry breaches and investigate the timing of those event with respect to when the flaws entered its database.
Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/securite-pc-et-internet/?&tag=DATA-BREACHES